Inside Gridinsoft:
Our Technology Stack
Under the Hood of Gridinsoft – Learn how our tools detect threats, protect users, and evolve with the cybersecurity landscape.
The beating heart of Gridinsoft's malware protection lies in its multi-layer scanning engine, responsible for detecting and eliminating threats across all platforms.
- Maintains a continuously updated database with millions of threat signatures.
- Updates occur hourly, ensuring coverage of newly discovered malware strains.
- Efficiently eliminates known threats with near-zero false positives.
- Offers remote access to Gridinsoft's scanning capabilities via RESTful API.
- Supports file hash lookups, URL analysis, and domain reputation checks.
- Built for scalability and speed — handles hundreds of concurrent queries with low latency.
- Analyzes file behavior in real-time based on rule sets and anomaly patterns.
- Flags suspicious actions, such as unauthorized process spawning or system modifications.
- Particularly effective against zero-day threats and polymorphic malware.
- Proprietary models (e.g., GANNet) trained on massive datasets of safe and malicious files.
- Detects anomalies and novel malware variants that evade traditional scanners.
- Continuously refined using threat intelligence feedback loops, reducing false positives and improving classification speed.
Threat Database / Reputation System
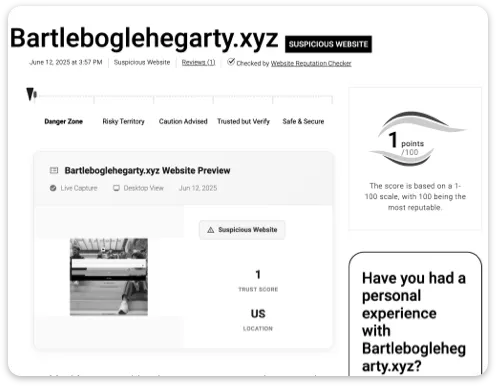
• Feeds key tools: Website Reputation Checker, Link Verity, and enhances on-device scans.
• Listed on VirusTotal: one of over 150 approved scanning engines.
Architecture & Deployment
Explore how Gridinsoft's technologies are delivered — from local tools to cloud-powered intelligence.
-
Desktop Application
• Windows-native solution with real-time file protection, heuristic defense, and flexible scanning options.
• Cloud-synced to ensure up-to-date detection without bloated system impact.
• Includes quarantine system, threat history, and scheduled scanning controls.
-
Trojan Killer Portable
• USB-run incident response toolkit: no installation, no internet required.
• Useful for on-site IT teams dealing with infected machines in isolated environments.
-
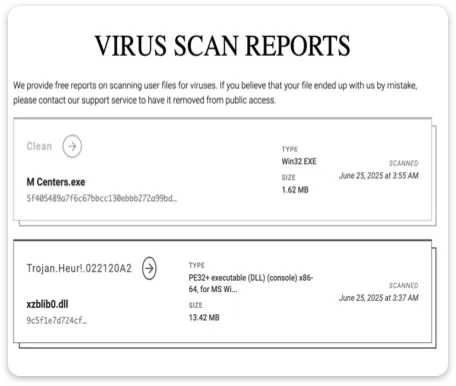
Threat Intelligence Reports
• Tools like Online Virus Scanner and Email Checker connect to Gridinsoft's secure cloud infrastructure.
• Input data is processed in memory, never stored, and scanned by the same engine that powers the desktop version.
• Results are returned in seconds with full HTTPS encryption.

Average scan time: ~7 minutes.
Typical result: detection of 29 threats, termination of 4 active malicious processes.
Optimized engine: lightweight on system resources, minimal memory usage.
-
Data Privacy
• No long-term storage of user-submitted files, URLs, or emails.
• All scans are executed transiently — no user-identifiable data is retained.
• Adheres to privacy-by-design principles and supports GDPR compliance.
-
Security of the Platform
• End-to-end SSL encryption between client tools and cloud servers.
• Infrastructure protected by advanced firewalls, frequent security audits, and strict access control.
-
False Positives and Transparency
• Preference for catching suspicious items (false positives) over missing dangerous ones.
• Users can easily report false positives via feedback tools.
• Public-facing knowledge base and support access ensure accountability.
• Over 17 years of development — continuously evolving since 2008.
• Trusted by over 480,000 users of our PC security tools worldwide.
View Verified Reviews →- In-house malware lab curates fresh samples daily from public and private feeds.
- Threat database updated hourly with user and partner submissions.
- R&D ongoing in scam pattern recognition, phishing email analysis, and social engineering detection.
- Language-based detection models for email phishing
- Behavioral baselining for fileless malware.
- Enhanced browser plugin protection modules.